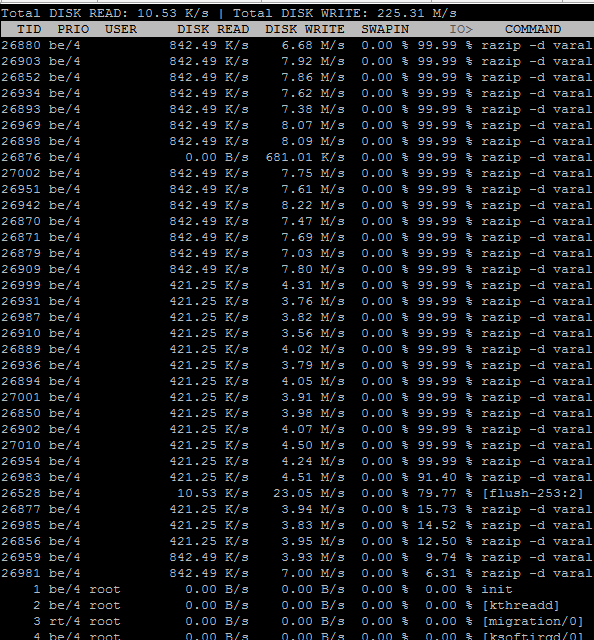
iotop for normal users
Posted on March 25, 2016 • 2 minutes • 223 words
Iotop doesn’t allow normal users to use this tool, this would be a security issue :
Netlink error: Operation not permitted (1)
The Linux kernel interfaces that iotop relies on now require root privileges
or the NET_ADMIN capability. This change occurred because a security issue
(CVE-2011-2494) was found that allows leakage of sensitive data across user
boundaries. If you require the ability to run iotop as a non-root user, please
configure sudo to allow you to run iotop as root.Please do not file bugs on iotop about this.
That’s good for security, but heck users can’t see if there process is IO bound … that’s crazy. Lucky you can just add the one exception without giving all the keys to the kingdom. (full sudo)
You could add a file to /etc/sudoers.d but you would need to adapt the /etc/sudoers anyway, so if you are not adding allot of users, (in my case one) just editing the file is also oké :
visudo
or if you don’t wanne use vi (don’t know how)
nano /etc/sudoers
just add this line :
user ALL=(ALL) NOPASSWD:/usr/sbin/iotop
from now on, users will be able to use :
sudo iotop
but not :
sudo yum remove gcc
Now users have the ability to follow if their processes are IO bound or not ! (note : might leak information)

 Buy me a Dr Pepper
Buy me a Dr Pepper